Beyond the Firewall: A Harborview Security Story
A scenario-based eLearning module designed to help non-technical small business employees understand what a firewall does, what it cannot do, and why their daily decisions matter for organizational security.

Overview
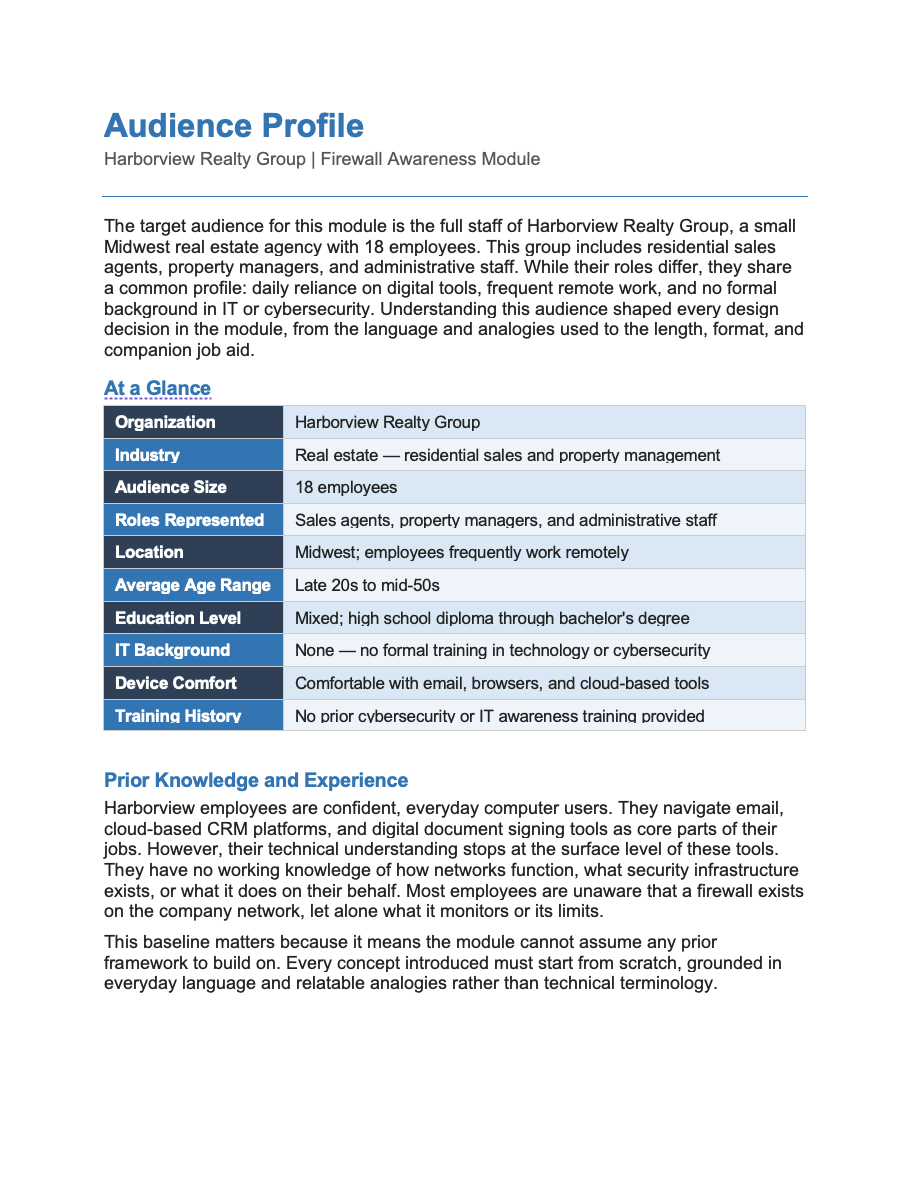
Audience: Sales agents, property managers, and administrative staff
Tools used: Adobe Captivate, Canva, Affinity Designer, Microsoft Office Suite
Harborview Realty Group is a boutique real estate agency based in the Midwest, specializing in residential home sales and property management. Harborview has 18 employees, including agents, administrative staff, and a small property management team. The company operates from a single office, but agents frequently work remotely from client properties, coffee shops, and home offices. The company relies heavily on email, a cloud-based CRM, and an online document signing platform to conduct daily business.
The Scenario
In early 2025, a Harborview agent received what appeared to be a routine email from a title company requesting updated wiring instructions for a pending closing. The agent, believing the email was legitimate, forwarded sensitive client financial information in response. The email was a spoofing attack; the sender was not the title company at all.
The incident prompted Harborview's office manager, Dana Kellerman, to work with an outside IT consultant to assess the company's security posture. The consultant confirmed that Harborview had a functioning firewall on its office network but identified a significant gap: employees did not understand what the firewall protected, what it did not cover, and how their own actions created risk. The consultant recommended a short security awareness training as a first step.
Dana engaged an instructional designer to develop the training to help all 18 employees build a foundational understanding of the firewall and their personal role in keeping client data secure.
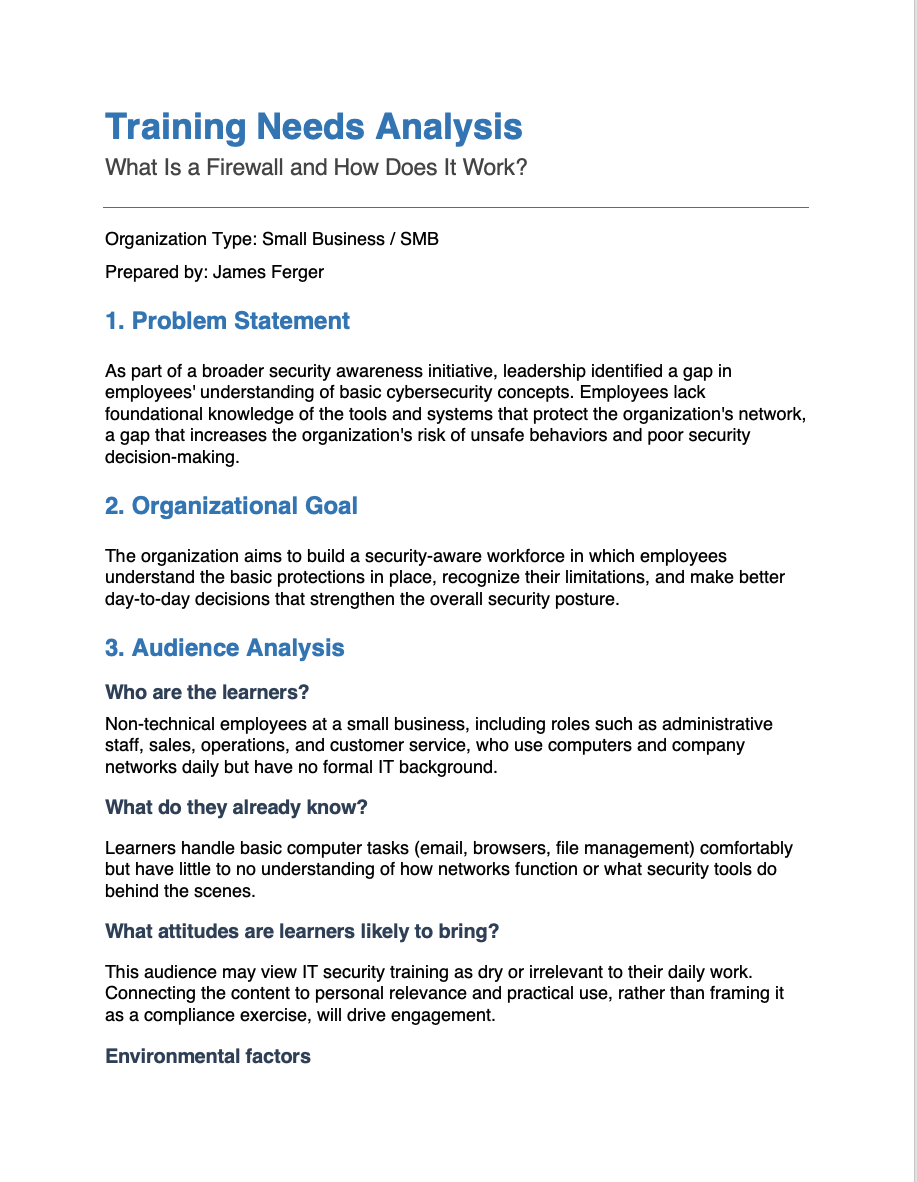
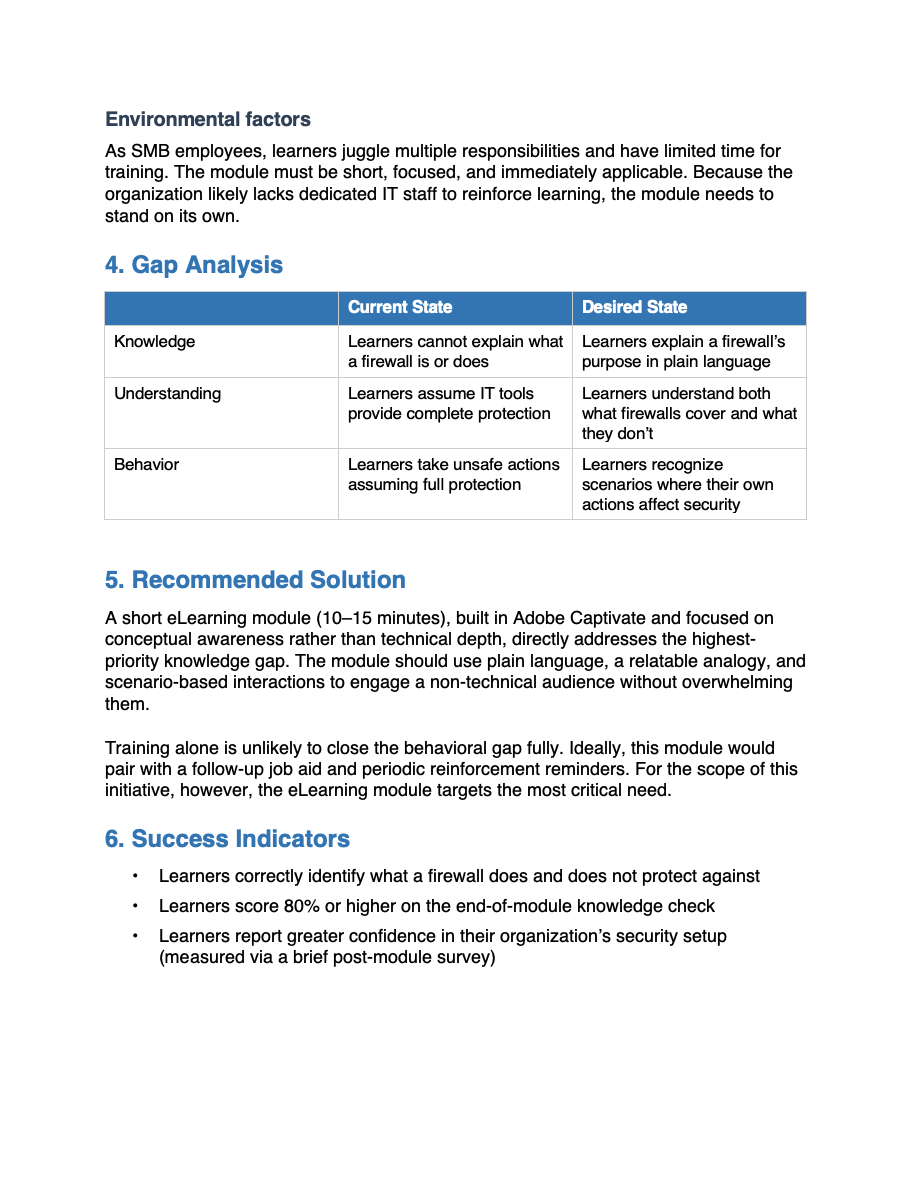
Needs Analysis Process
How I Identified the Need
This training did not originate from a routine curriculum review. A Harborview agent forwarded sensitive client financial information in response to a spoofed email, believing the request was legitimate. After the incident, office manager Dana Kellerman engaged an IT consultant to assess the company's security posture. The consultant confirmed that while Harborview had functioning security tools in place, employees lacked the foundational knowledge to understand what those tools did and, critically, what they could not do. The gap was not technological. It was instructional.
How I Gathered Information
I built the analysis on three inputs: a stakeholder interview with Dana Kellerman, the IT consultant's findings, and an audience profile I developed from both sources. The interview with Dana established that the company had never provided formal IT training, that employees ranged from administrative staff to remote field agents, and that the goal was awareness rather than technical proficiency. The consultant's findings identified the most critical gap: a widespread misconception that existing security tools provide complete protection.
What the Analysis Revealed
Three findings shaped the scope of the training. First, employees could not explain what a firewall is or how it works. Second, most believed that having security tools in place meant the organization was fully protected, a belief that eliminated any sense of personal accountability. Third, that misconception created direct behavioral risk, as the spoofing incident clearly demonstrated.
Employees were not being careless. They were operating without the information they needed to recognize risk. That distinction shaped the tone of the entire module.
How the Analysis Drove My Design Decisions
I connected each finding directly to a design choice. The knowledge gap led me to open the module with an analogy that builds a mental model before I introduced any technical content. The misconception finding made what a firewall cannot do, a non-negotiable inclusion rather than an afterthought. The behavioral risk pattern shaped the scenario-based knowledge check, where learners respond to situations that mirror the decisions they face in their actual work. The audience profile drove my choice of a 10-15-minute seat time, plain conversational language, and a companion job aid for employees working away from the office.
Every design decision in this module traces back to a specific finding. That traceability is the mark of needs-driven design.
Reflection
This project reinforced a principle central to my practice: training that does not rest on a clear understanding of the audience, the gap, and the context will not change behavior, regardless of how well it is designed. My goal was never to produce a module about firewalls. It was to help eighteen people make better decisions in moments that carry real consequences.
Audience Profile Process
How I Built the Profile
I built the audience profile from two sources. A stakeholder interview with Dana Kellerman identified the learners: 18 employees across sales, property management, and administrative roles, comfortable with everyday digital tools but completely unfamiliar with IT concepts. Dana also confirmed that no formal technology or security training had ever been provided. This was a first-exposure audience, not a refresher audience, and that distinction shaped every decision that followed.
The IT consultant's assessment added a critical layer. It identified not just what employees did not know, but what they incorrectly believed. That difference matters. A knowledge gap means a learner is missing information. A misconception is a belief that actively resists new information unless the design addresses it directly.
There is a difference between a learner who does not know something and a learner who believes the wrong thing. Designing for one when you have the other produces training that does not work.
What the Profile Revealed
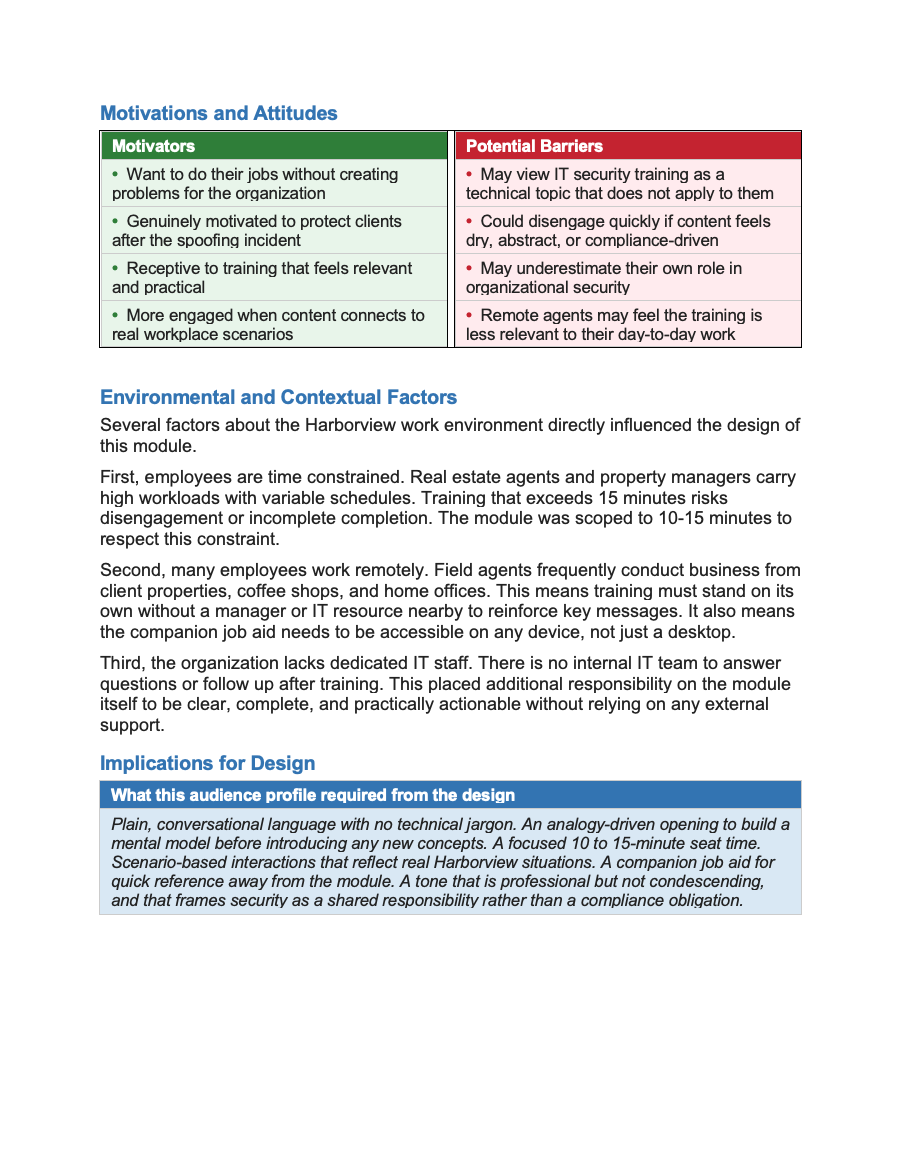
Four insights defined the design constraints for this project. First, the audience had no IT foundation to build on, so every concept had to connect to something learners already understood from everyday life. Second, most employees held a specific misconception — that existing security tools provided complete protection — a belief that required deliberate instructional attention to correct. Third, the audience was time-constrained, with demanding and variable schedules that made scope discipline non-negotiable. Fourth, many employees worked remotely without access to IT support, which meant the training needed to stand on its own and be supported by a portable reference tool.
How the Profile Drove My Design Decisions
Each insight connected directly to a design choice. The lack of an IT foundation led me to open the module with the security guard analogy, giving learners a mental model before I introduced any technical content. The misconception about complete protection made content a non-negotiable inclusion — a learner who finishes the module still believing the firewall handles everything has not been served by the training. The time constraint drove the 10-to-15-minute seat time and kept each slide focused on a single idea. The remote work reality drove the companion job aid, giving field agents a one-page reference they could access from any device without returning to the module.
Audience analysis does not just inform design; it shapes it. The audience analysis constrains the design in ways that make the final product more focused, more relevant, and more likely to change behavior.
Reflection
The Harborview audience profile reinforced a principle central to my practice: the most important thing I can know about a learning experience is who it is for. For this project, that meant designing for people who were not careless or indifferent to security, but who had simply never been given the information they needed to recognize risk. That framing shaped not just what I designed, but how I chose to speak to the learner throughout the entire module.